Table of Contents
HIPAA consists of complex sets of rules, which covered entities (CEs) and business associates (BAs) must adhere to in order to comply with federal regulations. One of the most important rules is the HIPAA Security Rule. The HIPAA Security Rule requirements ensure that both CEs and BAs protect patients’ electronically stored, protected health information (ePHI) through appropriate physical, technical, and administrative safeguards to fortify the confidentiality, integrity, and availability of ePHI.
The HIPAA Security Rule requirements are an extension to the protections contained in the Privacy Rule, which address technical and non-technical safeguards that every CEs must implement to secure ePHI.
The purpose of the HIPAA Security Rule
The rapid growth of technology has impacted the healthcare industry in many ways. A prime concern for healthcare providers is the safety and security of sensitive health information, as organizations shift towards paperless transactions and heavily rely on electronic information systems.
Healthcare organizations today use technologies in almost every aspect of their workflow, from electronic health records (EHR), biometric patient identification, and medical billing software to specialized technologies in pharmacies, and radiology for ensuring accurate treatment and patient diagnoses. While storing and transferring health information in electronic format has made life easier for physicians and enabled the smooth transition of workflow, it also poses serious security risks.
The HIPAA Security Rule requirements fulfill the purpose of protecting electronically stored health information while allowing CEs to adapt to new technologies to improve efficiency and quality of patient care. The Security Rule was designed to be flexible and scalable so that CEs can implement policies, procedures, and technologies that are appropriate according to their size, structure, and daily operations.
The HIPAA Security Rule Requirements
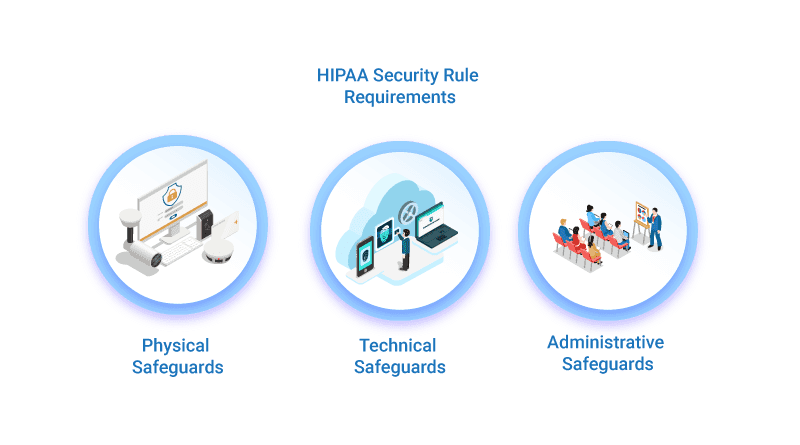
The requirements of the HIPAA Security Rule that CEs or BAs must address is broken down into three categories, which are:
Physical Safeguards
Physical safeguards involve implementing measures that protect the physical security of facilities where ePHI may be stored or maintained. Some common examples include:
- Alarm systems
- Surveillance cameras
- Restricting areas where ePHI is stored
Physical safeguards and control measures must include these standards:
Facility Access Controls: Covered entities and business associates must ensure that physical access to ePHI is restricted by allowing only authorized individuals to access information.
Workstation, Device, and Media Controls: CEs and BAs must:
- Implement appropriate policies and procedures specifying the proper functions that should be performed in workstations, how they should be performed, and how to access electronic devices.
- Have appropriate policies and procedures for transfer, disposal, removal, and re-use of electronic media.
Technical Safeguards
Technical safeguards involve adopting technologies and policies to protect data from unauthorized access. Examples of technical safeguards include data backup, firewalls, and encryption of devices to keep ePHI secure. Each covered entity needs to determine the appropriate level of safeguards that are necessary to protect ePHI in their organization. The requirements of technical safeguards as per the HIPAA Security Rule include the following:
Access controls: Implementing policies and procedures that allow access to systems containing ePHI only to authorized individuals.
Audit controls: Involves undertaking mechanisms that can record and examine activities in any information systems that use or contain ePHI, whether through software, hardware, or other mechanisms.
Integrity: Policies and procedures must be in place specifying that ePHI cannot in any way be improperly destroyed or altered.
Person or Entity Authentication: This involves implementing measures to verify the real identity of any individual or entity trying to access ePHI.
Transmission Security: This involves implementing measures to guard against unauthorized access when ePHI is in transmission.
Administrative Safeguards
Administrative safeguards include implementing employee policies and procedures to comply with the HIPAA Security Rule requirements. For instance, employee training, both for labor and management, defines what an individual can or cannot do once access is granted. Under the provisions of this safeguard, CEs and BAs are also required to perform risk analysis. Organizations need to ensure that they meet the required standards in the following areas:
Security Management Process: This involves the policies and procedures of organizations that pertain to security violations. It incorporates procedures for detecting, dealing with, and containing violations, and not just preventive measures.
Assigning Security Authority: This refers to the people or an individual assigned to develop and implement appropriate policies and measures to meet the requirements of the HIPAA Security Rule.
Security Awareness and Training: A critical component of HIPAA compliance is ensuring that employees, including those in management, undergo security training.
Security Incident Procedures: This involves the policies and procedures in place for dealing with security incidents.
Information Access Management: This refers to the level of authorization access to any ePHI, particularly how access is restricted to authorized individuals only.
Contingency Plan: This involves the course of actions for dealing with unanticipated occurrences or emergencies that might impair any of the systems that contain ePHI.
Evaluation: This involves evaluating the security plans and procedures to ensure that they are adequate. Performing security risk analysis also helps to assess what security measures are reasonable and appropriate, and more importantly, it helps to uncover gaps and vulnerabilities.
Business Associate Agreements and Other Arrangements: Covered entities must obtain assurance from their business associates before permitting them to create, maintain, receive, or transmit ePHI on their behalf. Business associates must be able to prove that information will always be appropriately safeguarded.
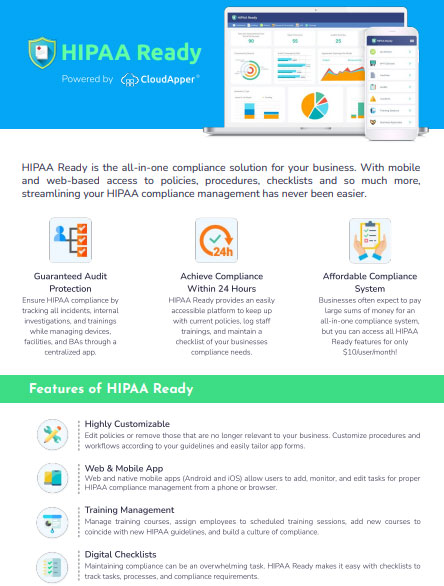
Comply Efficiently with HIPAA Ready
To comply with the HIPAA Security Rule requirements, covered entities also must perform a risk assessment to determine the threats or hazards to the security of ePHI. Performing these risk assessments regularly helps an organization steer clear of trouble. But trying to fulfill all the HIPAA Security Rule requirements is a painful proposition and this is why many organizations use the software, like HIPAA Ready.
HIPAA Ready is a robust, modern, cloud-based HIPAA compliance software that is designed to streamline compliance efforts by removing complications. From a single centralized platform, organizations can perform risk assessments, maintain documentation, set up training, manage incidents, and above all say goodbye to complexities!
Leave a comment to schedule a demo.
What is CloudApper AI Platform?
CloudApper AI is an advanced platform that enables organizations to integrate AI into their existing enterprise systems effortlessly, without the need for technical expertise, costly development, or upgrading the underlying infrastructure. By transforming legacy systems into AI-capable solutions, CloudApper allows companies to harness the power of Generative AI quickly and efficiently. This approach has been successfully implemented with leading systems like UKG, Workday, Oracle, Paradox, Amazon AWS Bedrock and can be applied across various industries, helping businesses enhance productivity, automate processes, and gain deeper insights without the usual complexities. With CloudApper AI, you can start experiencing the transformative benefits of AI today. Learn More