The rate of mobile phishing attacks has increased since the last quarter of 2019, a boost most likely attributed to the increased number of people working from home due to the COVID-19 crisis. Cybercriminals have changed their ways during the COVID-19 health crisis and are targeting remote workers, leveraging COVID-19 themed phishing website templates mimicking the World Health Organization (WHO), the Centers for Disease Control (CDC), and other agencies. According to a mobile security company Lookout, phishing attacks targeting mobile devices such as tablets and smartphones have surged in numbers. This is worrying for healthcare workers who are trying to treat patients from home using mobile devices. However, meeting certain HIPAA requirements can help healthcare providers ensure more security to their devices and increase awareness of risks. Let’s find out how.
Some important statistics
Mobile phishing attacks on corporate users have increased globally by 37.1 % between Q4 of 2019 and Q1 of 2020. Mobile phishing attacks in North America have increased by a bigger margin of 66.3%. Hackers are targeting remote workers in specific industries such as healthcare and the financial sectors.
Mobile phishing attacks have a higher success rate
Remote healthcare providers need to be extra vigilant with devices that contain electronic protected health information (ePHI) or they may risk disclosing all sorts of sensitive information to hackers. Meeting the HIPAA requirements is crucial as it ensures that users are implementing adequate safeguards and following proper security protocols. Phishing attacks on mobile device users have a higher success rate than when using a desktop or a laptop because users are more likely to click links that are malicious as they are harder to notice on smaller-sized screens.
Mobile devices show only the first part of the URL compared to a laptop or a desktop where the full URL might be displayed. This makes it easier for hackers to modify and make the URL appear more genuine on mobile devices. Also, mobile devices typically do not have the same security features as office computers or laptops, thus, phishing messages are less likely to be flagged and blocked out. In addition, there are more ways to deliver phishing URLs on mobile devices. On desktop computers, phishing URLs are mostly delivered via email, but on mobile devices, these URLs can be delivered via social media, messaging apps, SMS, and even dating apps. Mobile device users are more likely to click on these links without giving much thought, whereas, they would have been maybe more careful when using a desktop or laptop.
Meet HIPAA requirements with HIPAAReady for safer practice
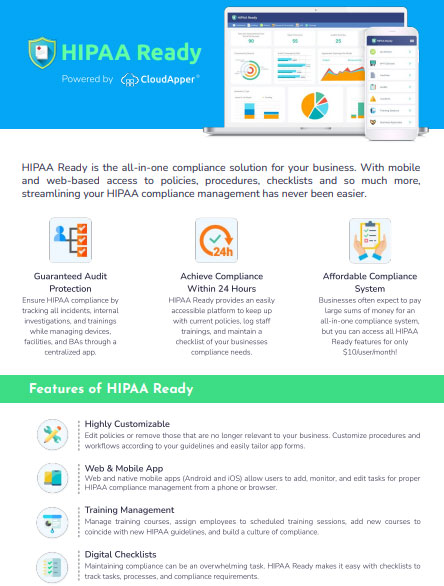
Meeting HIPAA requirements even while working from home has several benefits for healthcare workers. By taking necessary precautionary steps remote healthcare workers can better protect their devices that contain ePHI. Additionally, phishing attacks targeting mobile device users are a security concern that should be addressed by employers through proper education and security awareness training as per HIPAA requirements. However, every now and then there are new issues that need to be addressed through training due to fluctuating industry demands. Even so, software like HIPAAReady can guide your organization in the right direction by simplifying the whole training process.
HIPAAReady provides a comprehensive HIPAA compliance solution for organizations through a cloud-based application. With HIPAAReady, users can manage all the devices that contain ePHI and ensure that proper security is maintained. If users suspect any malicious actions and have doubts, they can also raise a concern through the application and receive proper guidance. HIPAAReady also allows users to regularly perform risk assessments and internal audits, which are all crucial to maintaining a high level of security.
What is CloudApper AI Platform?
CloudApper AI is an advanced platform that enables organizations to integrate AI into their existing enterprise systems effortlessly, without the need for technical expertise, costly development, or upgrading the underlying infrastructure. By transforming legacy systems into AI-capable solutions, CloudApper allows companies to harness the power of Generative AI quickly and efficiently. This approach has been successfully implemented with leading systems like UKG, Workday, Oracle, Paradox, Amazon AWS Bedrock and can be applied across various industries, helping businesses enhance productivity, automate processes, and gain deeper insights without the usual complexities. With CloudApper AI, you can start experiencing the transformative benefits of AI today. Learn More